Everything You Need to Close the Exposure Gap
Gain full visibility into your attack surface and eliminate critical exposures before attackers find them with our architectural approach to security.
Attack Surface Discovery
Continuous scanning and identification of all internet-facing assets, including shadow IT and unknown subdomains.
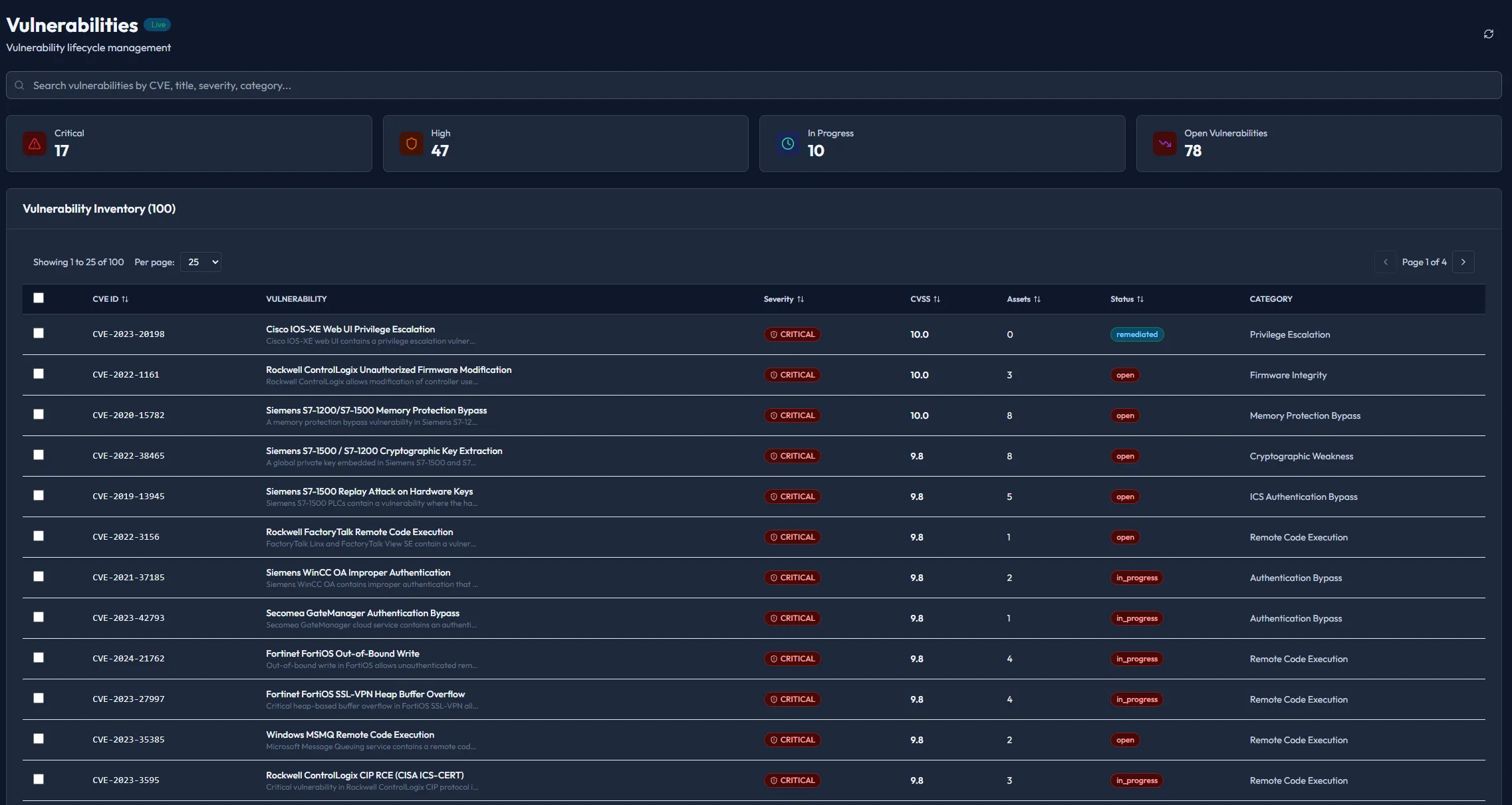
Attack Path Mapping & Prioritization
Visualize complex attack vectors and focus on what matters most.
- Real-time Vector Analysis
- Exploitability Scoring
- Blast Radius Mapping
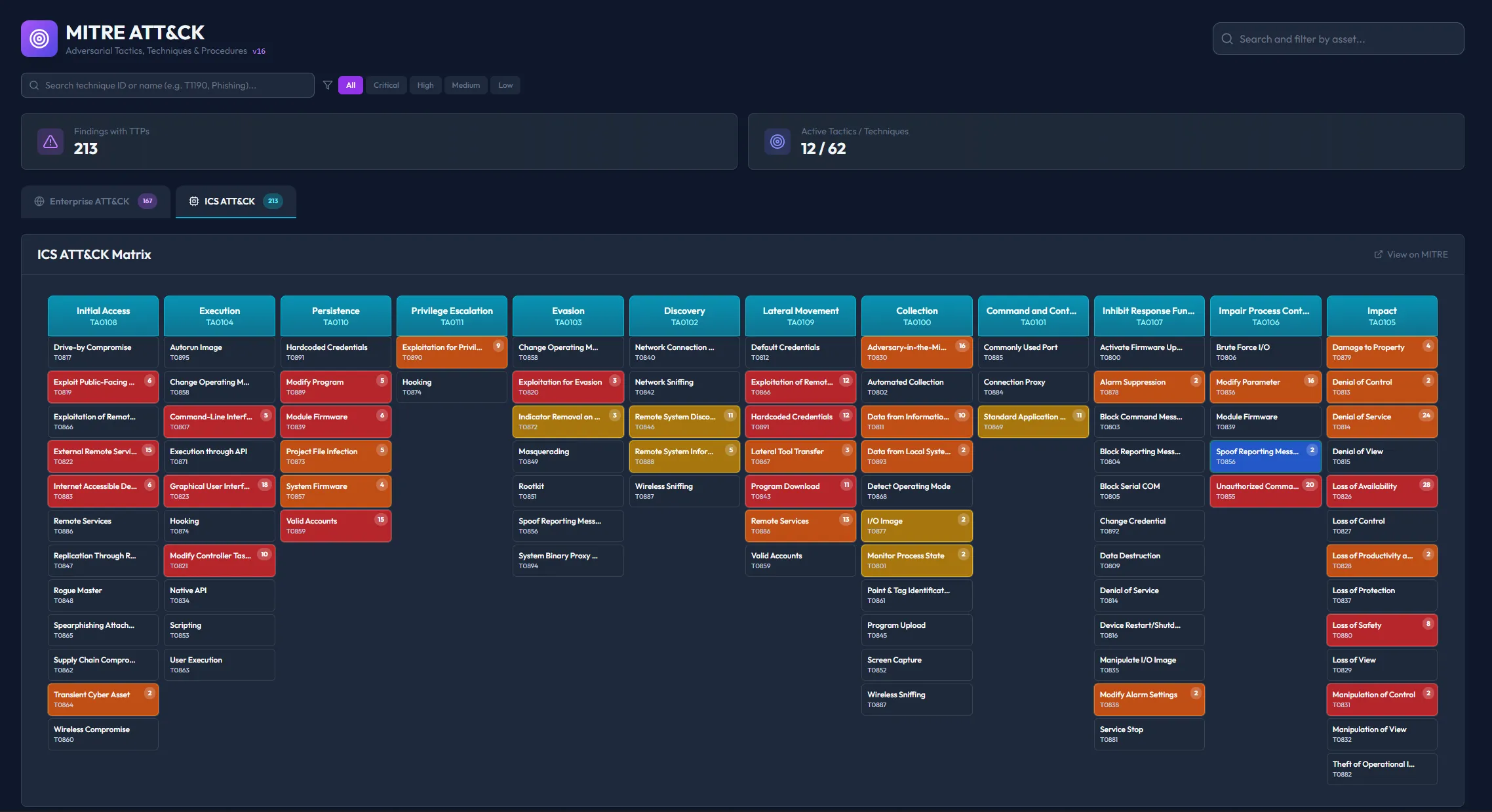
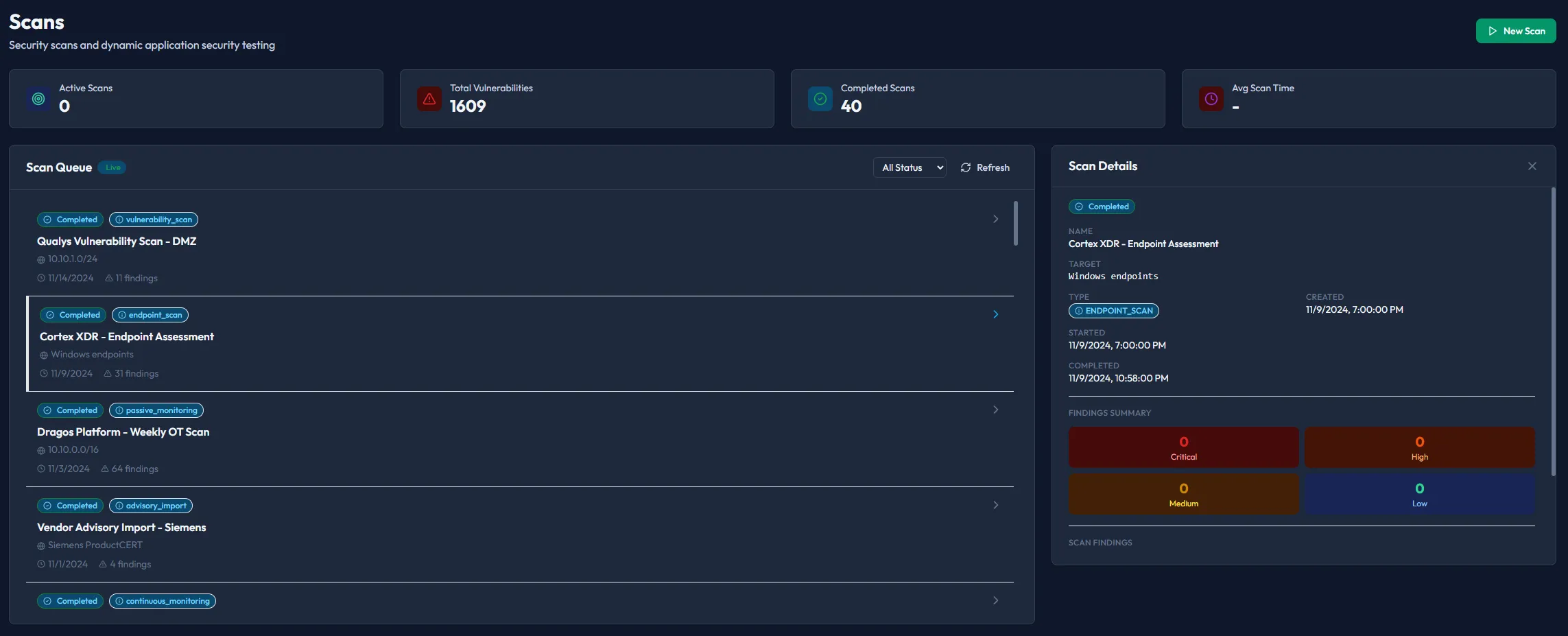
Continuous Validation & Attack Emulation
Safely replicate real-world adversary behavior to validate your security controls' effectiveness against the latest TTPs. Ensure your detection engineering is working as intended without disrupting operations.
Integrations
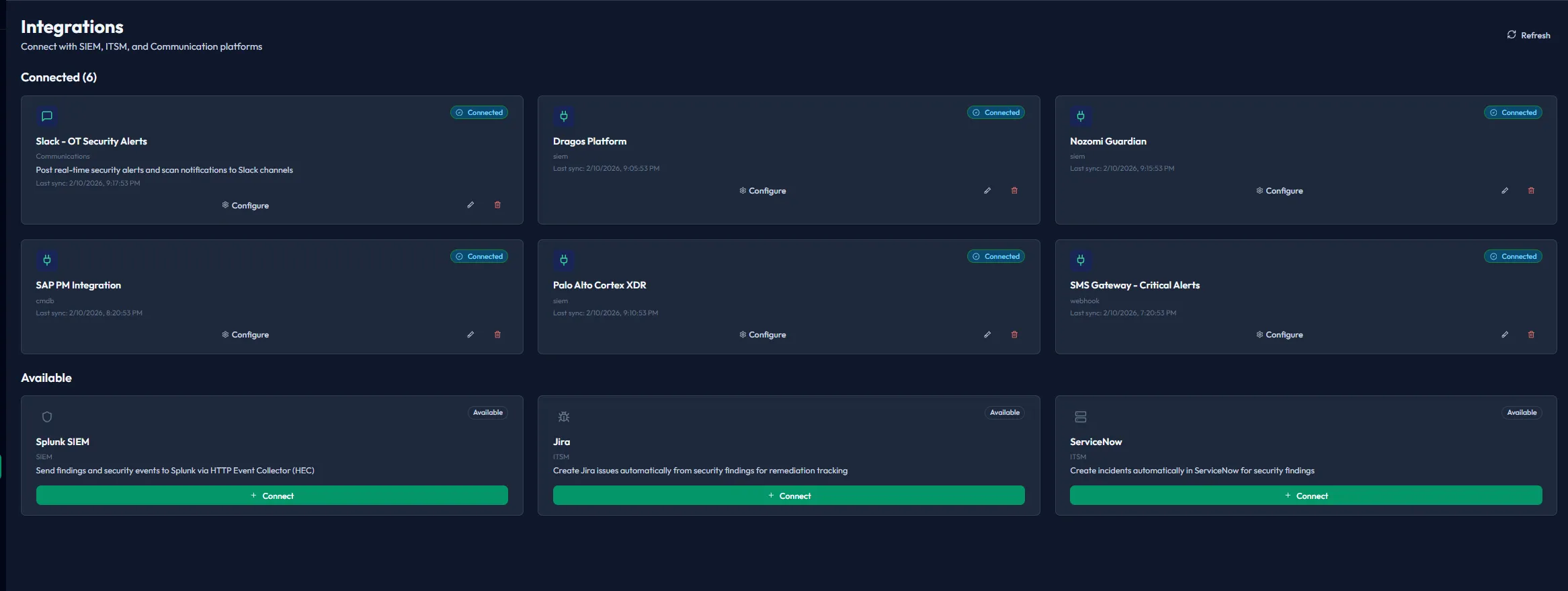
API & Webhooks
Programmatically interact with your exposure data. Our developer-first platform provides robust endpoints and powerful search capabilities for custom automation and reporting.
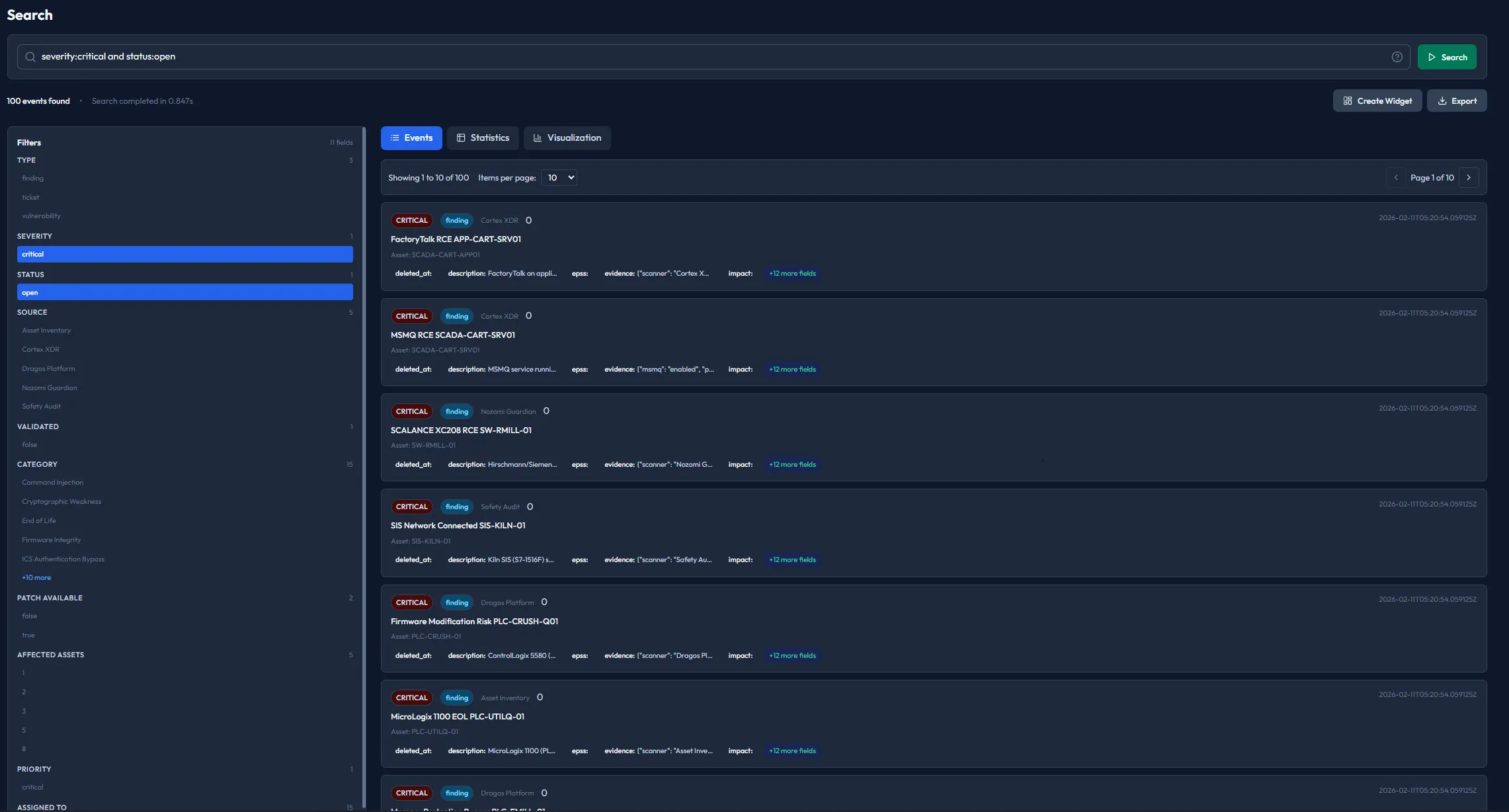
Global Semantic Search
Instantly query assets, findings, and emulations with our unified search layer.
{
"event": "exposure.critical",
"asset_id": "as_92kL10",
"severity": 9.8
}Architecture & Deployment
Flexibility designed for enterprise requirements.
SaaS
Full-managed cloud experience with instant scalability and zero maintenance overhead.
Hybrid
Maintain data sovereignty with on-prem collectors feeding into our secure analytics cloud.
On-premise
Air-gapped compatible deployment for the most sensitive government and finance networks.
Ready to Connect Your Stack?
Join forward-thinking security teams who've eliminated their visibility gaps.
Request a Demo